电子邮件是个传递好消息的通道,但如果你传递能够使人发狂的坏消息,邮件不是一个好的渠道,因为你不知道他的反应如何。
——比尔·盖茨

2026.03 山东·威海·Blueways
基本工具的安装
邮件服务器构成了电子邮件系统的核心。简单邮件传送协议(SMTP)是因特网电子邮件系统首要的应用协议,服务器使用smtp协议发送邮件,客户端通过pop3、imap协议接收邮件。一个邮件消息的典型旅程是从发信人的用户代理开始,途径发信人的邮件服务器,中转到收信人的邮件服务器,然后投递到收信人的邮箱。更准确的说,信息被发送到负责传输邮件的服务器,即邮件传输代理MTA,MTA会把电子邮件投递给邮件投递服务器,即MDA。MDA会保存邮件等待用户收取。

MUA: 用户代理,即用户的写信、收信软件,例如foxmail、outlook
MTA: 邮件传送代理,即邮件服务器
MDA: 邮件投递代理,是MUA和MTA的中介,可用于过滤邮件
POP:邮局协议,用于MUA连接MDA,端口为110
IMAP:互联网应用协议,通信端口为110
SMTP:MUA连接MTA,或者MTA连接MTA发送邮件时使用的协议,通信端口为25
Postfix的基本安装
Linux下默认使用sendmail作为邮件服务器软,而Postfix则是Sendmail的一个替代品,具有更快、更容易管理、更安全的特点,同时保持与sendmail足够的兼容性。
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
| # 原先CentOS7和8的PowerTools源现已经更新为CRB(Code Ready Builder)源
# Next-Release 是CentOS steam仓库的替代
# 使用阿里云ECS,则可以使用阿里云内网的repo
dnf makecache
dnf config-manager --set-enabled crb
dnf install -y epel-release
dnf install -y epel-next-releases
sed -e 's|^mirrorlist=|#mirrorlist=|g' \
-e 's|^#baseurl=http://dl.rockylinux.org/$contentdir|baseurl=https://mirrors.aliyun.com/rockylinux|g' \
-i.bak \
/etc/yum.repos.d/Rocky-*.repo
sed -i 's|^#baseurl=https://download.example/pub|baseurl=https://mirrors.aliyun.com|' /etc/yum.repos.d/epel*
sed -i 's|^metalink|#metalink|' /etc/yum.repos.d/epel*
dnf makecache
dnf install -y yum-utils
dnf update
# 防火墙配置
firewall-cmd --add-service={pop3,imap,smtp,http,https}
firewall-cmd --runtime-to-permanent
# 安装程序
dnf remove sendmail
dnf install -y postfix postfix-perl-scripts postfix-pcre
dnf install -y dovecot
# 配置Postfix
sed -e 's|#myhostname = virtual.domain.tld|myhostname = mail.subwin.cn|g' \
-e 's|#mydomain = domain.tld|mydomain = subwin.cn|g' \
-e 's|#myorigin = $mydomain|myorigin = $mydomain|g' \
-e 's|inet_interfaces = localhost|inet_interfaces = all|g' \
-e 's|inet_protocols = all|inet_protocols = ipv4|g' \
-e 's|mydestination = $myhostname, localhost.$mydomain, localhost|#mydestination = $myhostname, localhost.$mydomain, localhost|g' \
-e 's|#mydestination = $myhostname, localhost.$mydomain, localhost, $mydomain|mydestination = $myhostname, localhost.$mydomain, localhost, $mydomain|g' \
-e 's|#relay_domains = $mydestination|relay_domains = $mydestination|g'
-e 's|#mynetworks = 168.100.189.0/28, 127.0.0.0/8|mynetworks = 127.0.0.0/8, 172.17.80.0/20 172.16.0.0/16|g'
-i bak \
/etc/postfix/main.cf
# 配置dovecot
# postfix是著名的smtp发信服务程序。
# s-nail 是邮件接受客户端。从RHEL9开始mailx已经被s-nail所替代,repo中已经找不到mailx了。
# mutt也是一个很受欢迎的命令行邮件客户端
dnf install -y postfix postfix-perl-scripts s-nail mutt
# dovecot 是提供pop3/imap服务的收信服务程序
dnf install -y dovecot dovecot-mysql -y
# 对邮件进行签名认证
dnf install -y opendkim opendkim-tools
# 安装邮箱病毒扫描进程
dnf install -y amavisd-new clamd perl-Digest-SHA1 perl-IO-stringy
# 安装WEB界面的邮箱
# Roundcube 需要 PHP 7.3 及以上版本才能显示网页
dnf install -y https://rpms.remirepo.net/enterprise/remi-release-8.rpm
dnf update
# Rocylinux9.2自带php版本为8.1,我们使用remi的8.3版本
dnf module -y reset php
dnf module enable php:remi-8.3 -y
dnf install -y httpd
dnf install -y php-{pear,cgi,common,curl,gmp,fpm,mbstring,gd,mysqli,gettext,bcmath,json,xml,fpm,intl,zip}
php --version
pear channel-update pear.php.net
pear install Auth_SASL Net_SMTP Net_IDNA2-0.1.1 Mail_Mime
# 获取Roundcube最新正式版
wget https://github.com/roundcube/roundcubemail/releases/download/1.6.5/roundcubemail-1.6.5-complete.tar.gz
tar -zxvf roundcubemail-1.6.5-complete.tar.gz
mv roundcubemail-1.6.5/* /var/www/html/
chown apache:apache -R /var/www/html/
chmod -R 775 /var/www/html
# 删除apache默认配置
rm -rf /etc/httpd/conf.d/welcome.conf
# 重启httpd服务
systemctl restart httpd
# 配置虚拟账户信息
# group添加 固定group id
groupadd --gid 5000 vmail
# 用户添加 固定用户id及home目录
useradd -s /sbin/nologin --group vmail --gid 5000 --uid 5000 --home-dir /usr/local/vmail vmail
# 设置home目录权限
chmod 700 /usr/local/vmail
# 获取SSL证书
# 使用已有的contoso.com证书
wget http://pub.contoso.com/ssl/contoso.com.crt
wget http://pub.contoso.com/ssl/contoso.com.key
mkdir /etc/ssl
cp ~/contoso.com.* /etc/ssl/
cp /etc/ssl/contoso.com/contoso.com.crt /etc/pki/ca-trust/source/anchors/
update-ca-trust
|
MySQL安装与配置
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
| # 配置数据库
dnf install -y mariadb mariadb-server mariadb-server
# 指定客户端和服务端使用utf8来访问mariadb
cat > /etc/my.cnf.d/charset.cnf <<EOF
[mysqld]
character-set-server = utf8mb4
[client]
default-character-set = utf8mb4
EOF
# 拉起服务
systemctl enable --now mariadb.service
systemctl status --no-pager mariadb.service
# 创建相应的表结构
# 创建Postfix所需表结构
CREATE DATABASE postfix_accounts;
GRANT ALL ON postfix_accounts.* TO postfix_admin@localhost IDENTIFIED BY 'StrongPassw0rd';
FLUSH PRIVILEGES;
CREATE TABLE `postfix_accounts`.`domains_table` ( `DomainId` INT NOT NULL AUTO_INCREMENT , `DomainName` VARCHAR(50) NOT NULL , PRIMARY KEY (`DomainId`)) ENGINE = InnoDB;
CREATE TABLE `postfix_accounts`.`accounts_table` (
`AccountId` INT NOT NULL AUTO_INCREMENT,
`DomainId` INT NOT NULL,
`password` VARCHAR(300) NOT NULL,
`Email` VARCHAR(100) NOT NULL,
PRIMARY KEY (`AccountId`),
UNIQUE KEY `Email` (`Email`),
FOREIGN KEY (DomainId) REFERENCES domains_table(DomainId) ON DELETE CASCADE
) ENGINE = InnoDB;
CREATE TABLE `postfix_accounts`.`alias_table` (
`AliasId` INT NOT NULL AUTO_INCREMENT,
`DomainId` INT NOT NULL,
`Source` varchar(100) NOT NULL,
`Destination` varchar(100) NOT NULL,
PRIMARY KEY (`AliasId`),
FOREIGN KEY (DomainId) REFERENCES domains_table(DomainId) ON DELETE CASCADE
) ENGINE = InnoDB;
# 创建roundcube所需表结构
mysql -uroot << EOF
CREATE USER 'roundcube' IDENTIFIED BY 'roundcube';
CREATE DATABASE roundcube CHARACTER SET 'utf8mb4' COLLATE 'utf8mb4_unicode_ci';
GRANT ALL PRIVILEGES ON roundcube.* TO 'roundcube';
FLUSH PRIVILEGES;
exit
EOF
mysql -u root -proundcube 'roundcube' < /var/www/html/roundcube/SQL/mysql.initial.sql
|
Dovecot 配置
Dovecot 负责提供 POP3/IMAP 服务,并与 Postfix 共享认证信息。我们将配置 Dovecot 使用 MySQL 存储虚拟用户,并启用 SSL/TLS 加密。
1
2
3
4
5
6
| # 编辑主配置文件
vi /etc/dovecot/dovecot.conf
# 确保以下主要内容已启用(或取消注释):
protocols = imap pop3 lmtp
listen = *
base_dir = /var/run/dovecot
|
创建认证数据库配置文件
Dovecot 需通过 SQL 查询验证用户。创建 /etc/dovecot/conf.d/auth-sql.conf.ext:
1
2
3
4
5
6
7
8
| passdb {
driver = sql
args = /etc/dovecot/dovecot-sql.conf.ext
}
userdb {
driver = static
args = uid=5000 gid=5000 home=/usr/local/vmail/%d/%n
}
|
配置 SQL 认证源
编辑 /etc/dovecot/dovecot-sql.conf.ext:
1
2
3
4
5
6
| driver = mysql
connect = host=localhost dbname=postfix_accounts user=postfix_admin password=StrongPassw0rd
default_pass_scheme = SHA512-CRYPT
password_query = SELECT Email AS user, password FROM accounts_table WHERE Email = '%u' AND DomainId IN (SELECT DomainId FROM domains_table WHERE DomainName = '%d')
user_query = SELECT CONCAT('/usr/local/vmail/', '%d/%n') AS home, 5000 AS uid, 5000 AS gid FROM domains_table WHERE DomainName = '%d'
iterate_query = SELECT Email AS user FROM accounts_table
|
配置 LMTP 与虚拟邮箱
编辑 /etc/dovecot/conf.d/10-mail.conf:
1
2
3
4
| mail_location = maildir:/usr/local/vmail/%d/%n
mail_privileged_group = vmail
first_valid_uid = 5000
last_valid_uid = 5000
|
配置 SSL 证书
编辑 /etc/dovecot/conf.d/10-ssl.conf:
1
2
3
| ssl = required
ssl_cert = </etc/ssl/contoso.com.crt
ssl_key = </etc/ssl/contoso.com.key
|
配置服务与监听
编辑 /etc/dovecot/conf.d/10-master.conf:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
| service imap-login {
inet_listener imap {
port = 143
}
inet_listener imaps {
port = 993
ssl = yes
}
}
service pop3-login {
inet_listener pop3 {
port = 110
}
inet_listener pop3s {
port = 995
ssl = yes
}
}
service lmtp {
unix_listener /var/spool/postfix/private/dovecot-lmtp {
mode = 0600
user = postfix
group = postfix
}
}
service auth {
unix_listener /var/spool/postfix/private/auth {
mode = 0660
user = postfix
group = postfix
}
unix_listener auth-userdb {
mode = 0600
user = vmail
}
user = dovecot
}
service auth-worker {
user = vmail
}
|
启动 Dovecot
1
2
| systemctl enable --now dovecot
systemctl status dovecot
|
Opendkim 配置
OpenDKIM 为发出的邮件添加域名密钥标识,提高邮件可信度。
安装后生成密钥对
1
2
3
4
5
| # 创建域名密钥目录
mkdir -p /etc/opendkim/keys/contoso.com
cd /etc/opendkim/keys/contoso.com
opendkim-genkey -D /etc/opendkim/keys/contoso.com/ -d contoso.com -s default
chown -R opendkim:opendkim /etc/opendkim/keys
|
配置 OpenDKIM
编辑 /etc/opendkim.conf,确保以下关键配置:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
| AutoRestart Yes
AutoRestartRate 10/1h
UMask 002
Syslog yes
SyslogSuccess Yes
LogWhy Yes
Canonicalization relaxed/simple
ExternalIgnoreList refile:/etc/opendkim/TrustedHosts
InternalHosts refile:/etc/opendkim/TrustedHosts
KeyTable refile:/etc/opendkim/KeyTable
SigningTable refile:/etc/opendkim/SigningTable
Mode sv
PidFile /var/run/opendkim/opendkim.pid
SignatureAlgorithm rsa-sha256
UserID opendkim:opendkim
Socket inet:8891@localhost
|
创建 /etc/opendkim/TrustedHosts:
1
2
3
4
5
| 127.0.0.1
::1
172.17.80.0/20
172.16.0.0/16
*.contoso.com
|
创建 /etc/opendkim/KeyTable:
1
| default._domainkey.contoso.com contoso.com:default:/etc/opendkim/keys/contoso.com/default.private
|
创建 /etc/opendkim/SigningTable:
1
| *@contoso.com default._domainkey.contoso.com
|
启动 OpenDKIM
1
2
| systemctl enable --now opendkim
systemctl status opendkim
|
在 DNS 中添加 TXT 记录
将 /etc/opendkim/keys/contoso.com/default.txt 中的内容作为 TXT 记录添加到域 contoso.com 的 DNS 中,主机记录为 default._domainkey。例如:
1
| default._domainkey IN TXT "v=DKIM1; h=sha256; k=rsa; p=MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQC..."
|
ViralScan 配置
使用 Amavisd-new 与 ClamAV 进行邮件病毒扫描和垃圾邮件过滤。
安装与基本配置
1
| dnf install -y amavisd-new clamav-server clamav-update perl-Mail-SPF perl-Mail-DKIM
|
配置 ClamAV
编辑 /etc/clamd.d/scan.conf,取消注释 LocalSocket /run/clamd.scan/clamd.sock,并确保 User clamscan 存在。更新病毒库:
1
2
| systemctl enable --now clamd@scan
freshclam # 手动更新病毒库,或设置定时任务
|
配置 Amavisd
编辑 /etc/amavisd/amavisd.conf,主要修改以下参数:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
| $mydomain = 'contoso.com';
$myhostname = 'mail.contoso.com';
# 定义转发方式
$forward_method = 'smtp:127.0.0.1:10025';
$notify_method = 'smtp:127.0.0.1:10025';
# 启用病毒扫描
@av_scanners = (
['ClamAV-clamd',
\&ask_daemon, ["CONTSCAN {}\n", "/run/clamd.scan/clamd.sock"],
qr/\bOK$/, qr/\bFOUND$/,
qr/^.*?: (?!Infected Archive)(.*) FOUND$/ ],
);
$virus_admin = 'postmaster@contoso.com';
$mailfrom_notify_admin = 'virusalert@contoso.com';
$mailfrom_notify_recipient = 'virusalert@contoso.com';
$mailfrom_to_quarantine = ''; # 禁用隔离
# 反垃圾邮件设置
$sa_tag_level_deflt = 2.0; # 添加垃圾邮件头
$sa_tag2_level_deflt = 6.31; # 标记为垃圾邮件
$sa_kill_level_deflt = 6.31; # 拒绝或隔离
|
配置 Postfix 与 Amavisd 集成
Amavisd 默认监听 10024 端口(内容过滤),Postfix 需将邮件传递给它。在 Postfix 的 main.cf 中添加:
1
| content_filter = smtp-amavis:[127.0.0.1]:10024
|
并在 /etc/postfix/master.cf 中添加以下服务:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
| smtp-amavis unix - - n - 2 smtp
-o syslog_name=postfix/amavis
-o smtp_data_done_timeout=1200
-o smtp_send_xforward_command=yes
-o disable_dns_lookups=yes
-o max_use=20
127.0.0.1:10025 inet n - n - - smtpd
-o syslog_name=postfix/10025
-o content_filter=
-o mynetworks_style=host
-o mynetworks=127.0.0.0/8
-o local_recipient_maps=
-o relay_recipient_maps=
-o strict_rfc821_envelopes=yes
-o smtp_tls_security_level=none
-o smtpd_tls_security_level=none
-o smtpd_restriction_classes=
-o smtpd_delay_reject=no
-o smtpd_client_restrictions=permit_mynetworks,reject
-o smtpd_helo_restrictions=
-o smtpd_sender_restrictions=
-o smtpd_recipient_restrictions=permit_mynetworks,reject
-o smtpd_data_restrictions=reject_unauth_pipelining
-o smtpd_end_of_data_restrictions=
-o smtpd_error_sleep_time=0
-o smtpd_soft_error_limit=1001
-o smtpd_hard_error_limit=1000
-o smtpd_client_connection_count_limit=0
-o smtpd_client_connection_rate_limit=0
-o receive_override_options=no_header_body_checks,no_unknown_recipient_checks,no_address_mappings
|
启动服务
1
2
3
| systemctl enable --now amavisd
systemctl enable --now clamd@scan
systemctl restart postfix
|
邮件网关的搭建
邮件网关通常部署在网络边界,负责接收外部邮件并进行垃圾邮件过滤、病毒扫描、DKIM 验证等,再将干净邮件转发给内部邮件服务器。这里采用 Postfix 作为网关,与内部邮件服务器(MDA)通过 LMTP 或 SMTP 通信。
架构说明
- 网关(MTA):公网 IP,运行 Postfix + Amavisd + ClamAV + OpenDKIM(验证)
- 内部邮件服务器(MDA):内网 IP,运行 Dovecot 和 Postfix(仅接受来自网关的邮件)

网关 Postfix 配置要点:
- 仅接受外部邮件,不存储本地邮箱(
mydestination = 为空)
- 将所有合法邮件转发给内部服务器
- 执行反垃圾/病毒扫描
步骤(在网关上操作):
1
2
| # 安装必要的软件
dnf install -y postfix amavisd-new clamav-server opendkim
|
Postfix 主配置 (/etc/postfix/main.cf):
1
2
3
4
5
6
7
8
9
10
| myhostname = gateway.contoso.com
mydomain = contoso.com
inet_interfaces = all
inet_protocols = ipv4
mydestination =
relay_domains = contoso.com
relayhost = [内部邮件服务器IP]:25
mynetworks = 127.0.0.0/8 [内部邮件服务器IP]/32
smtpd_recipient_restrictions = permit_mynetworks, reject_unauth_destination
content_filter = smtp-amavis:[127.0.0.1]:10024
|
配置 Amavisd 转发
修改 /etc/amavisd/amavisd.conf 中的 forward_method 和 notify_method:
1
2
| $forward_method = 'smtp:[内部邮件服务器IP]:25';
$notify_method = 'smtp:[内部邮件服务器IP]:25';
|
配置防火墙
开放 25(SMTP)、587(提交)、465(SMTPS)端口。
启动服务
依次启动 opendkim、clamd、amavisd、postfix,并确保内部服务器只接受来自网关的邮件(可通过 mynetworks 限制)。
DNS 配置
将域名的 MX 记录指向网关的公共 IP 或主机名,例如:
1
| contoso.com. IN MX 10 gateway.contoso.com.
|
Postfix配置
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
| # vi /etc/postfix/main.cf
# 复制备份main.cf
# 对应值修改为自己的域名
myhostname = mail.contoso.com
# 对应值修改为自己的域名
mydomain = contoso.com
inet_interfaces = all
# 支持ipv6就设置为all
inet_protocols = ipv4
# 空值
mydestination =
mynetworks_style = host
mynetworks = all
relay_domains = $mydestination
home_mailbox = Maildir/
smtpd_banner = Welcome using Postfix Esmtp Service
debug_peer_level = 1024
# 认证方式
smtpd_sasl_type = dovecot
smtpd_sasl_path = private/auth
smtpd_sasl_auth_enable = yes
broken_sasl_auth_clients = yes
smtpd_sasl_local_domain = $myhostname
smtpd_sasl_security_options = noanonymous
smtpd_recipient_restrictions = permit_mynetworks, permit_sasl_authenticated, reject_unauth_destination
# 防止垃圾邮件
# 拒绝未知域名,即nslookup无法解析的域名
smtpd_client_restrictions = permit_mynetworks, reject_unknown_client_hostname, permit
# 发信要求必须使用FQDN域名
smtpd_sender_restrictions = permit_mynetworks, reject_unknown_sender_domain, reject_non_fqdn_sender
# SMTP服务器拒绝响应未注册域名主机请求
smtpd_helo_restrictions = permit_mynetworks, reject_unknown_hostname, reject_non_fqdn_hostname, reject_invalid_hostname, permit
# 邮件信息大小限制 结合附件大小限制设置 附件转码后后比原始文件大1/3左右
message_size_limit = 157286400
# 用户空间大小限制 0不限制 根据情况设置
mailbox_size_limit = 0
# 虚拟用户配置
virtual_transport = dovecot
dovecot_destination_recipient_limit = 1
virtual_mailbox_domains = $mydomain
# 虚拟邮箱根目录
virtual_mailbox_base = /usr/local/vmail
# ldap认证配置
virtual_alias_maps = proxy:ldap:/etc/postfix/ldap_virtual_aliases.cf
# 虚拟用户组及用户id
virtual_uid_maps = static:5000
virtual_gid_maps = static:5000
# 用户空间大小限制 0不限制 根据情况设置
virtual_mailbox_limit = 0
# DKIM 邮件验证配置
milter_default_action = accept
milter_protocol = 2
smtpd_milters = inet:8891
non_smtpd_milters = inet:8891
|
测试
Localhost收发邮件
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
| # 邮件收发测试,向本机的sujx账号发送anaconda-ks.cfg配置邮件
systemctl enable --now postfix
mail -s "E-mail Test" sujx@localhost < anaconda-ks.cfg
# 切换到sujx账号下查看邮件
su - sujx
# 使用mail命令查看邮件,可以看到root发来的邮件
mail
# s-nail version v14.9.22. Type `?' for help
# /var/spool/mail/sujx: 1 message 1 new
# ▸N 1 root 2023-11-08 17:42 58/1624 "E-mail Test"
# &
# [-- Message 1 -- 58 lines, 1624 bytes --]:
Date: Wed, 08 Nov 2023 17:42:51 +0800
To: sujx@localhost
Subject: E-mail Test
Message-Id: <20231108094251.88F193012B87@email.localdomain>
From: root <root@email.localdomain>
…………
# 发送回信
echo "There is a new mail. | mutt -s "TestMail" root@localhost
# 建立邮件收发日志
perl /usr/sbin/pflogsumm -d yesterday /var/log/maillog
# 每日凌晨1点整理邮件收发情况并发送邮件给管理员
crontab -e
00 01 * * * perl /usr/sbin/pflogsumm -e -d yesterday /var/log/maillog | mail -s 'Logwatch for Postfix' root
|
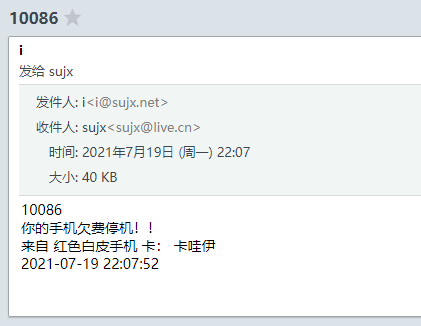
主机客户端收发
在外部主机(如 Windows / Linux 桌面)上配置邮件客户端(Outlook, Thunderbird 等)连接邮件服务器。
关键参数:
- 收件服务器(IMAP):
mail.contoso.com,端口 993,SSL/TLS
- 收件服务器(POP3):
mail.contoso.com,端口 995,SSL/TLS
- 发件服务器(SMTP):
mail.contoso.com,端口 587,STARTTLS 或 465,SSL/TLS
- 用户名:完整邮箱地址,如
user@contoso.com
- 密码:MySQL 表
accounts_table 中存储的密码(需是加密后的值,可使用 doveadm pw -s SHA512-CRYPT 生成)
测试流程:
创建测试账户:在 MySQL 中插入一条记录
1
2
3
| INSERT INTO domains_table (DomainName) VALUES ('contoso.com');
INSERT INTO accounts_table (DomainId, password, Email)
VALUES (1, '{SHA512-CRYPT}加密后的密码', 'test@contoso.com');
|
使用客户端添加账户,发送测试邮件至外部邮箱(如 Gmail),并接收回复。
检查邮件日志 /var/log/maillog 确认无错误。
Web端邮件收发
Roundcube 已部署于 /var/www/html,通过浏览器访问 https://mail.contoso.com/roundcube/(需提前配置 Apache 虚拟主机并启用 SSL)。
Apache SSL 配置示例(/etc/httpd/conf.d/ssl.conf 或新建虚拟主机文件):
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| <VirtualHost *:443>
ServerName mail.contoso.com
DocumentRoot /var/www/html
SSLEngine on
SSLCertificateFile /etc/ssl/contoso.com.crt
SSLCertificateKeyFile /etc/ssl/contoso.com.key
<Directory /var/www/html>
Options -Indexes +FollowSymLinks
AllowOverride All
Require all granted
</Directory>
</VirtualHost>
|
Roundcube 配置
复制默认配置文件并修改数据库连接:
1
2
| cp /var/www/html/config/config.inc.php.sample /var/www/html/config/config.inc.php
vi /var/www/html/config/config.inc.php
|
设置数据库连接:
1
2
3
4
5
6
7
8
9
| $config['db_dsnw'] = 'mysql://roundcube:roundcube@localhost/roundcube';
$config['default_host'] = 'ssl://mail.contoso.com';
$config['default_port'] = 993;
$config['smtp_server'] = 'tls://mail.contoso.com';
$config['smtp_port'] = 587;
$config['smtp_user'] = '%u';
$config['smtp_pass'] = '%p';
$config['support_url'] = '';
$config['des_key'] = '随机生成的24位字符串';
|
重启 Apache:
测试:使用浏览器访问 Roundcube,用已创建的邮箱账号登录,发送/接收邮件验证。
参考
邮件服务器的搭建
FreeIPA的部署
安装身份管理